
Yesterday, the Bush Administration released a long awaited report by the Environmental Protection Agency, that says that Carbon Dioxide can and should be regulated. One would think this a remarkable departure for an administration that has done everything within its power to destroy the environment, through drilling in fragile environmental areas, unmitigated logging, and the failure to protect endangered species. There’s a catch: the Supreme Court ordered the EPA to develop the report, and in releasing it, in the same breath, the administration argued that regulation by the EPA to protect our children will hurt business and industrial growth.
Let’s review our tally for this administration:
- Housing — Failure to properly regulate the housing market has led to a massive series of bank failures.
- The Energy Market — we are suffering from inflation due to a massive increase in oil prices, which itself is in part due to an inability of Americans to conserve. The administration has done absolutely nothing to reduce consumption, or for that matter offer fuel alternatives. Instead, they’ve argued that drilling in wilderness refuges will offer some form of relief, a claim that is disputed by every expert in the field, because it will offer no short term relief, while medium and long term relief are by no means at all assured.
- Security— having gone to war twice and wasted billions of dollars on meaningless programs, the administration has managed to alienate America from the rest of the world, reducing people’s desires to visit, impacting tourism, and reducing our national credibility. At the same time the Taliban has rebuilt itself, and we’ve lost our allies in Pakistan and now, seemingly Iraq (not that Prime Minister Maliki was every clearly an ally).
- Education— No Child Left Behind has meant that our children haven’t gone forward as a group. Our public education system remains in a shambles due to lack of incentives for good teachers, buildings that are falling apart, and a general willingness by this administration to divert funds to religious programs.
- Public Transportation— our skies are more dangerous than they have been since the creation of the FAA. More runway incursions, more close calls in the air, disgruntled workforces, and disgruntled passengers have left our air transportation system in a mess, while we’ve invested nearly nothing in ground public transport.
- Public Welfare— with a remarkably lame response to Hurricane Katrina, the administration demonstrated that they could not be trusted with emergency crisis management.
In short, they did nothing except collect pay checks. Perhaps Americans will pay more attention to our civic responsibilities the next time we hand someone the keys.
 Often times it is said that the purpose of academic research is to seek the truth, no matter where it leads. The purpose of industry representatives is often to obscure the truths they do not like. Such apparently was the case at a recent hearing of the Texas House of Representatives’
Often times it is said that the purpose of academic research is to seek the truth, no matter where it leads. The purpose of industry representatives is often to obscure the truths they do not like. Such apparently was the case at a recent hearing of the Texas House of Representatives’  There are those who think, “Oh cool, Eclipse. Let’s all party and watch the {sun|moon} disappear for a few minutes.” And then there are those who are serious about it. While we all were celebrating the 4th of July (wherever we were), several friends of mine were busy getting themselves and a lot of provisions onto a plane to China in order to observe the upcoming
There are those who think, “Oh cool, Eclipse. Let’s all party and watch the {sun|moon} disappear for a few minutes.” And then there are those who are serious about it. While we all were celebrating the 4th of July (wherever we were), several friends of mine were busy getting themselves and a lot of provisions onto a plane to China in order to observe the upcoming 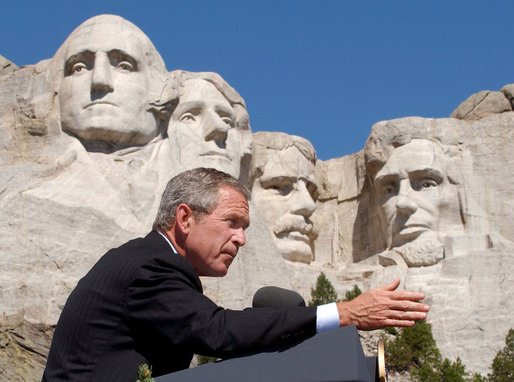 Continuing our theme from Independence Day, let’s talk about freedoms and rights. For those such as Alan Dershowitz who advocate such things as
Continuing our theme from Independence Day, let’s talk about freedoms and rights. For those such as Alan Dershowitz who advocate such things as  Happy Fourth of July! 232 years ago, descendants of peopel seeking religious freedom declared that they would not be subjugated from afar by a tyrant and his parliament.
Happy Fourth of July! 232 years ago, descendants of peopel seeking religious freedom declared that they would not be subjugated from afar by a tyrant and his parliament.